Tag Cloud
Currently Reading
Latest Book Reviews
- Certified Kubernetes Application Developer (CKAD) Study Guide, 2nd Edition Posted on January 11, 2025
- Rancher Deep Dive Posted on March 31, 2023
- Leveraging Kustomize for Kubernetes Manifests Posted on March 24, 2023
- Automating Workflows with GitHub Actions Posted on October 13, 2022
- Deep-Dive Terraform on Azure Posted on August 30, 2022 All Book Reviews
Latest Posts
- Locking Down Drupal Access with Nginx Posted on November 9, 2015
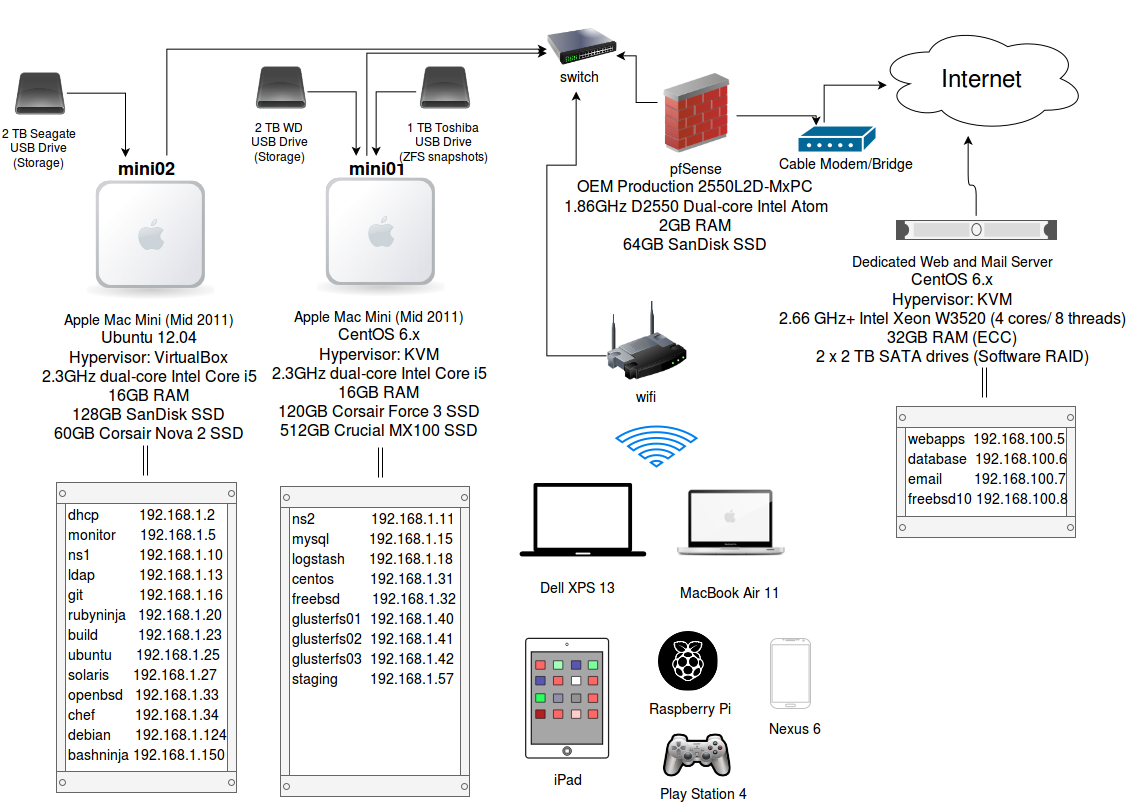
- My Home Lab Network Diagram Posted on October 31, 2015
- Grepping for PHP system level command functions Posted on September 20, 2015
- Setting up Graphite on CentOS 6.x gotcha Posted on September 12, 2015
- VirtualBox: Increase guest VM CPU count Posted on July 18, 2015
November 9, 2015
Locking Down Drupal Access with Nginx
by Alpha01
This site is powered by Drupal. Drupal and WordPress for that matter, are well targeted platforms, mainly because of their large install base on the internet. Quite frankly the reason I bother using both Drupal and WordPress instead of a flat-file based CMS is because I have to deal with these web applications at work on a daily basis, so it’s a great way to keep myself current with the technology that’s paying my bills.
I have Nginx acting as an SSL proxy for www.rubysecurity.org, which is hosted on an Apache back-end. So I have a few configs that I’ve enabled to lock down access to my Drupal site. The configs are made at the Nginx proxy level, so they can never reach Apache.
Firstly, I have all of Drupal’s /admin locked out from outside access:
location = /admin {
allow MY-HOME-IP-ADDRESS;
deny all;
return 403;
}
Next, I only allow login access from my home ip address:
location = /user {
allow MY-HOME-IP-ADDRESS;
deny all;
proxy_pass https://www.rubysecurity.org/user;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header Host $http_host;
}
Lastly, since Nginx is unable to process query strings at the location block level, I’ve setup an additional config to drop all user login query requests.
if ($args ~* "q=user") {
set $blockme M;
}
if ($remote_addr != MY-HOME-IP-ADDRESS) {
set $blockme "${blockme}E";
}
if ($blockme = ME) {
return 403;
}
security nginx drupal October 31, 2015
My Home Lab Network Diagram
by Alpha01
It’s Friday night, I don’t have anything interesting to do, so I created a diagram of my current home lab setup.
Tags: [ubuntu networking kvm virtualbox September 20, 2015
Grepping for PHP system level command functions
by Alpha01
grep --color -r -E -e '(escapeshellarg|escapeshellcmd|exec|passthru|proc_close|proc_get_status|proc_nice|proc_open|proc_terminate|shell_exec|system)(\s+)?\(' ./
php security September 12, 2015
Setting up Graphite on CentOS 6.x gotcha
by Alpha01
I installed graphite-web via the EPEL repo, and I was getting an 500 error when accessing the Graphite web interface.
Error
[Sat Sep 12 00:56:27 2015] [error] [client 192.168.1.21] mod_wsgi (pid=17318): Exception occurred processing WSGI script '/usr/share/graphite/graphite-web.wsgi'.
[...]
[Sat Sep 12 00:56:27 2015] [error] [client 192.168.1.21] File "/usr/lib/python2.6/site-packages/django/db/backends/sqlite3/base.py", line 344, in execute
[Sat Sep 12 00:56:27 2015] [error] [client 192.168.1.21] return Database.Cursor.execute(self, query, params)
[Sat Sep 12 00:56:27 2015] [error] [client 192.168.1.21] DatabaseError: attempt to write a readonly database
Fix
It turns out the sqlite3 database file Graphite write’s too, was owned by root. So it was simply a matter of updating the ownership to what ever user Apache is running under, in my case it’s apache.
chown -R apache.apache /var/lib/graphite-web/
centos monitoring July 18, 2015
VirtualBox: Increase guest VM CPU count
by Alpha01
Syntax
VBoxManage modifyvm <VMNAME> –cpus <CPUcount>
tony@mini02:~$ VBoxManage showvminfo monitor | grep "Number of CPUs"
Number of CPUs: 1
tony@mini02:~$ VBoxManage modifyvm monitor --cpus 3
tony@mini02:~$ VBoxManage showvminfo monitor | grep "Number of CPUs"
Number of CPUs: 3
virtualbox